6 min read
Cyber Threat Intelligence Report
This week, we briefed our clients on the second-most-active Ransomware-as-a-Service organization, The Gentleman. We describe their observed TTPs.
5 min read
 PacketWatch Team Sixty43
:
October 23, 2023
PacketWatch Team Sixty43
:
October 23, 2023

Welcome back to another week of Cyber Threat Intelligence (CTI). This week's report highlights two critical zero-days from Cisco and critical vulnerabilities in Citrix NetScaler.
Last week, Cisco published a security advisory highlighting a critical (CVSS 10.0) zero-day vulnerability in the Cisco IOS XE software.
Tracked as CVE-2023-20198, successful exploitation of this vulnerability allows for a remote unauthenticated attacker to create an account on the system with 'level 15 access'. This permission set allows the user to enter 'Privileged Exec' mode and provides complete control over the device.
Devices in the wild that have been successfully compromised were found to have a malicious Lua (programming language) implant installed that allows for additional access to the system.
It was initially believed that successful installation of this implant was related to a previous Cisco vulnerability, CVE-2023-1435; however, it was later disclosed that a second 0-day, CVE-2023-20273 was being leveraged to install the implant.
Heading into the weekend, internet scanners showed approximately 60,000 devices had been successfully compromised and showed evidence of the malicious implant.
On Sunday, October 22, that number dropped substantially, down to less than 1,000.
Security researchers are unsure as to why this number dropped so significantly, but one of the leading theories is the threat actor updated the implant code and configuration so that it is not as simple to detect remotely.
This vulnerability affects Cisco IOS XE Software if the Web UI feature is enabled, including enterprise switches, access points, wireless controllers, and routers. This feature is enabled via the ‘ip http server’ or ‘ip http secure-server’ commands.
Per the Cisco advisory, administrators can determine whether the HTTP server is enabled on a system by running the following command:
show running-config | include ip http server|secure|active
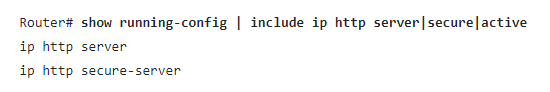
Fig. 1: Router command per Cisco advisory
Note: Per the advisory, the presence of either command or both commands in the system configuration indicates the Web UI feature is enabled.
Additionally:
To determine if a vulnerable system may have already been compromised, administrators can perform the following checks:
Review system logs to check for any log messages where user could be cisco_tac_admin, cisco_support, or “any configured, local user that is unknown to the network administrator”:
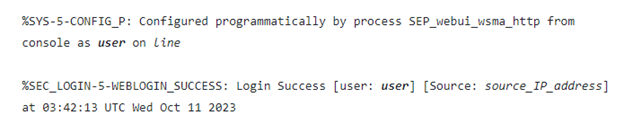 Fig. 2: Cisco system log example
Fig. 2: Cisco system log example
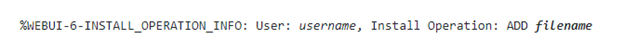 Fig. 3: Cisco system log for file "implant" install
Fig. 3: Cisco system log for file "implant" install
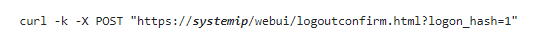 Fig. 4: Curl request to check for implant (per Cisco)
Fig. 4: Curl request to check for implant (per Cisco)
As of October 22, Cisco has begun rolling out official fixes for affected product versions. Additional details and the full patch release schedule can be found here.
Until all affected devices can be fully patched and remediated, system administrators are strongly encouraged to identify all Cisco devices that have the HTTP Server feature enabled and disable it. If disabling the HTTP Server is not feasible, then strict access control lists can also mitigate exploitation. Only allow trusted hosts and networks to connect to the device. All identified devices should be thoroughly checked for evidence of the malicious implant and for unauthorized accounts.
Additional Resources
On October 10, Citrix released a security bulletin highlighting two vulnerabilities in the NetScaler ADC and NetScaler Gateway platforms.
The first, CVE-2023-4966, carries a critical CVSS rating of 9.4, and is an "unauthenticated buffer-related vulnerability" that can lead to "sensitive information disclosure".
While the original bulletin from Citrix did not disclose what information could be leaked via exploitation, security firm Mandiant has since published documentation stating successful exploitation allows the threat actor to "hijack existing authenticated sessions, bypassing multifactor authentication (MFA) or other authentication requirements". These sessions may also persist even after the patch has been deployed.
The second vulnerability, CVE-2023-4967, carries a high-severity CVSS rating of 8.2, and is a denial of service (DoS) vulnerability. It should be noted that the device must be configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or an AAA virtual server in order to be vulnerable.
The bulletin applies to customer-managed NetScaler ADC and NetScaler Gateway products:
Note: NetScaler ADC and NetScaler Gateway version 12.1 are now End-of-Life (EOL) and are vulnerable.
Administrators are strongly encouraged to patch vulnerable devices as soon as possible. A full list of current firmware versions can be found here. In addition to patching, Mandiant has provided additional steps to ensure persistent access to a compromised device has been removed:
Additional Resources
PacketWatch publishes this report and other cybersecurity threat intel to the security community for free via our blog. If you want personalized threat intel, contact us today to learn about our enterprise threat intelligence services.
Kindly be advised that the information contained in this article is presented with no final evaluation and should be considered raw data. The sole purpose of this information is to provide situational awareness based on the currently available knowledge. We recommend exercising caution and conducting further research as necessary before making any decisions based on this information.

6 min read
This week, we briefed our clients on the second-most-active Ransomware-as-a-Service organization, The Gentleman. We describe their observed TTPs.

10 min read
This week, we briefed our clients on Anthropic's announcement of Claude Mythos Preview and its alleged ability to discover and exploit...

7 min read
This week, we briefed our clients on recent supply chain attacks to raise awareness and help organizations identify whether they have been attacked.